Rev’s Transcript Library
Explore our extensive collection of free transcripts from political figures and public events. Journalists, students, researchers, and the general public can explore transcripts of speeches, debates, congressional hearings, press conferences, interviews, podcasts, and more.

Police Week Memorial Ceremony
Immigration and Customs Enforcement holds a memorial ceremony for fallen officers. Read the transcript here.

Anti-Fraud Press Conference
J.D. Vance holds a press conference on Anti-Fraud initiatives. Read the transcript here.

COVID-19 Whistleblower Hearing
A COVID-19 whistleblower testifies before the Senate Homeland Security Committee. Read the transcript here.

Army Budget Hearing
Army Secretary Driscoll testifies on budget request in Senate hearing. Read the transcript here.
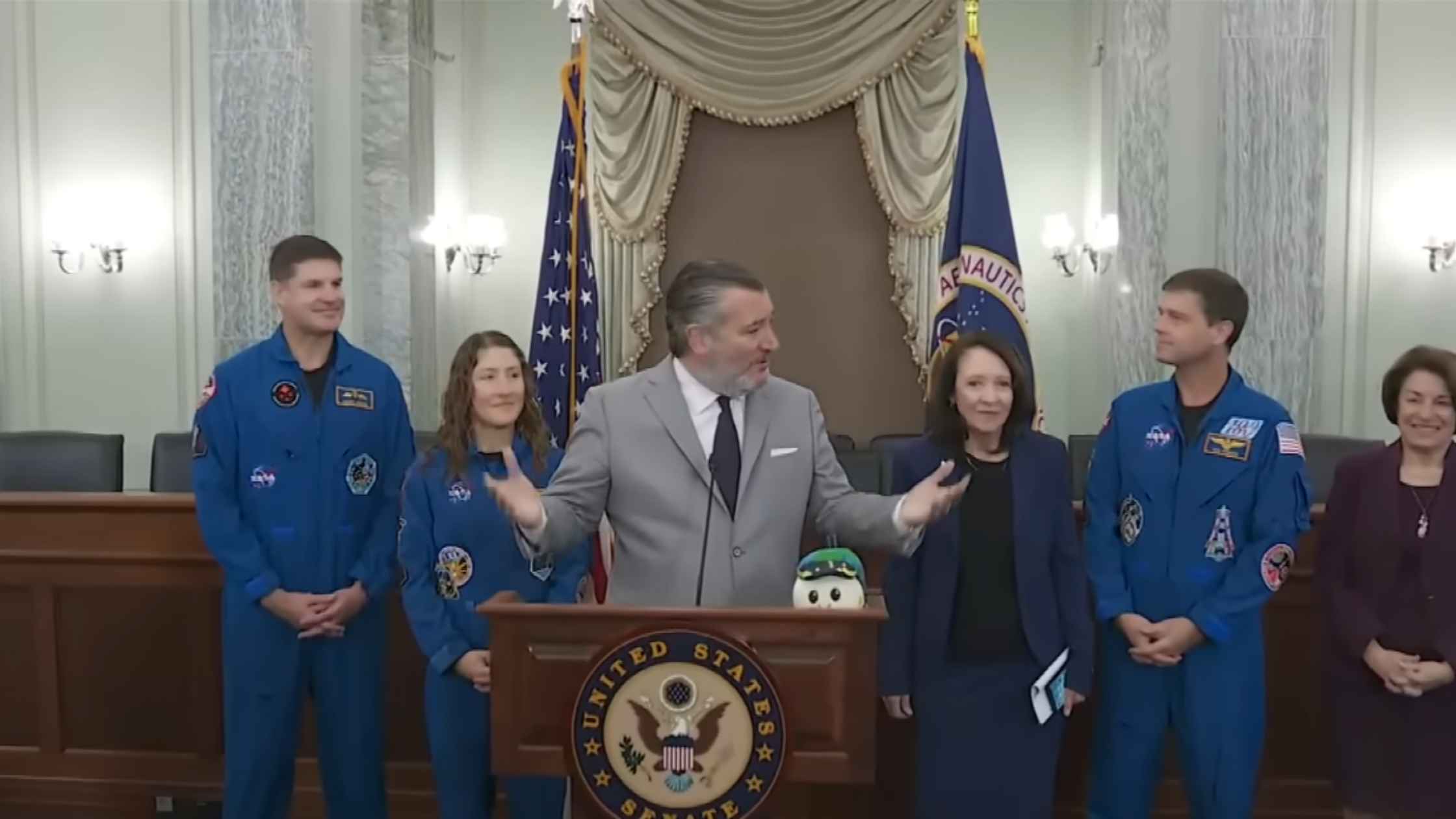
Artemis II Astronauts on Capitol Hill
The Senate Commerce, Science, & Transportation Committee hosts members of the NASA Artemis II crew at the Capitol. Read the transcript here.

Department of Defense Budget Hearing
Pete Hegseth and Dan Caine testify on the DOD budget request before Congress. Read the transcript here.

Epstein Survivors Testify Publicly Before House Committee
The House Committee on Oversight and Government Reform hears from Epstein survivors. Read the transcript here.

Ball State University Commencement
Actor Hugh Jackman delivers the 2026 commencement address for Ball State University. Read the transcript here.

2026 Emerson College Commencement Address
Henry Winkler delivers the commencement address to 2026 Emerson College graduates. Read the transcript here.

Indiana Hoosiers Visit the White House
The White House hosts the 2026 college football national champions, the Indiana Hoosiers. Read the transcript here.
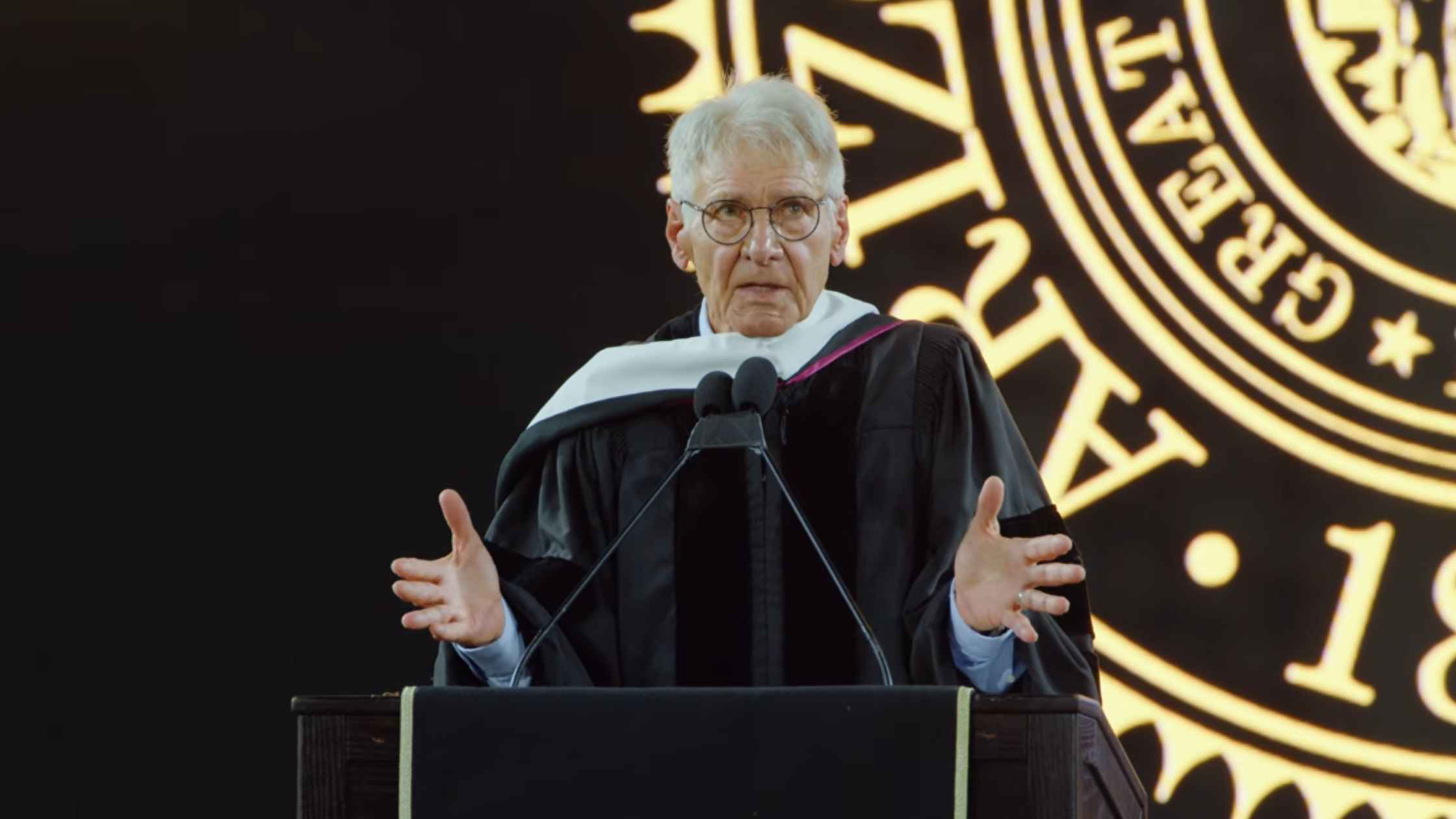
Arizona State Commencement Speach 2026
Actor Harrison Ford delivers the commencement address at Arizona State University. Read the transcript here.

Americans from Hantavirus-hit Cruise Ship Arrive in Nebraska
Nebraska medical officials hold a briefing about the hantavirus outbreak and the U.S. passengers who were evacuated. Read the transcript here.
Subscribe to The Rev Blog
Sign up to get Rev content delivered straight to your inbox.